CONFidence 2019 – conference recap
Every year CONFidence is one of the most important events for us and is supported by our entire team.
We prepare substantive lectures, meet with clients, and at the same time we try to surprise the participants, challenge the more and less advanced of them, and get everyone interested.
Here you can read about last year’s CONFidence edition.
Our presentations
Attacking AWS: the full cyber kill chain,Paweł Rzepa
The aim of the presentation was to show the difference between safety assessment in a “cloud” infrastructure and test environments in a classical architecture. Paweł involved the audience in an interactive sample attack on a company in AWS environment. The participants voted and decided live about the events.

Attacking AWS Workshop, Paweł Rzepa
In addition to the presentation, Paweł also prepared a few hours of workshops. During the workshops, the participants could test live examples of how to detect and use configuration errors in AWS-based services

As a supplement to the presentations and workshops, we recommend downloading the guide: Seven-Step Guide to SeCuring your AWS Kingdom and reading an article about cloud infrastructure pentesting.
We need to go deeper – testing inception apps, Jakub Kałużny
Jakub introduced the attendees to the world of “inception apps” with multiple layers of obfuscation, encoding and encryption. He pointed out technical aspects of this type of security, but also the process of organizing penetration tests in special-risk applications. Currently, they often do not include the fact that the testing team may need additional time to deobfuscate communication before even starting the tests.

SecuNicornz Challenge
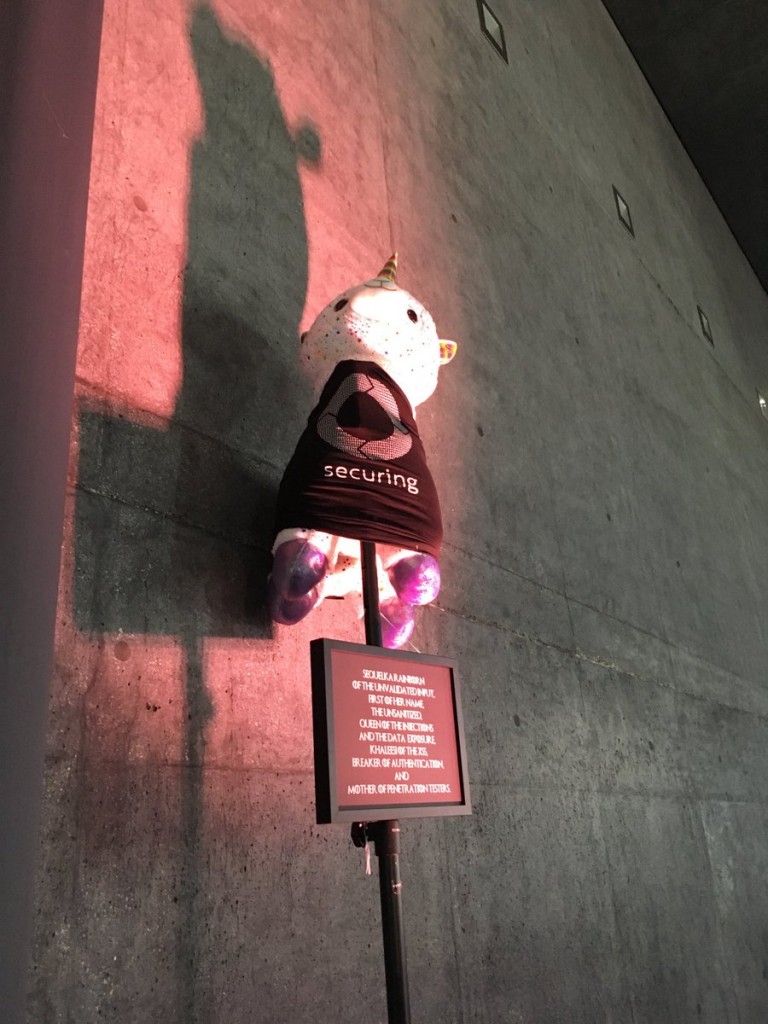
As every year, our stand offered a challenge.
Last year during the SecuRadar Challenge, we focused on the old good XSS susceptibility. This year’s unicorns were just a cover for SQL Injection. What was the challenge?
Using a QR code you had to register your “unicorn” in the application. Unicorns were assigned different weight, and the aim was to hunt the most valuable ones. To make the task harder, the most valuable unicorns belonged to the SecuRing team! So the best hackers who managed to take over our unicorns were rewarded with presents – each of them chose a prize for himself. In addition, at the end of the second day of the conference, the guys whose unicorns were at the top of the list won tickets for the next CONFidence edition.
Security Playground


Fingerprint cloning, NFC cards and alarm blocking – that’s what we prepared for the participants in our Security Playground. Everyone could try their hand as a hacker – some of you were really impressed!
We would like to thank all CONFidence participants and … see you next year!



